Okay, so check this out—DeFi governance and liquidity design aren’t separate puzzles. Wow! They’re braided together. Medium-sized token holdings can sway votes. Long-term tokenomics, the incentives of liquidity providers, and subtle mechanics like weight changes in a pool all interact in ways that reward some actors and penalize others, often simultaneously and unexpectedly.
At first glance governance looks simple: holders vote, proposals pass, changes happen. Initially I thought that would be enough—pure democracy on-chain. But then I realized that turnout is terrible, and vote-buying strategies make outcomes more plutocratic than democratic. My instinct said the problem was just apathy, but actually, wait—let me rephrase that: apathy is part of it, and so is the design of token distribution and the liquidity primitives used during launch.
Here’s the thing. Liquidity Bootstrapping Pools (LBPs) change initial price discovery by shifting token weights over time. Really? Yes. LBPs start with imbalanced weights that slide toward a more neutral composition, which pushes token prices down as supply becomes easier to acquire. This is clever. It fights simple pump-and-dump tactics. At the same time it creates a new set of governance questions: who gets tokens early, and who gets voting power later?
LBPs were popularized for fairer launches. In practice they reduce early monopolies because the initial high prices discourage instant sniping. On one hand LBPs can democratize allocation. On the other hand, they reward those who can monitor—and act—during weight transitions. Hmm…
Where governance meets liquidity: practical mechanics
Governance isn’t just about votes. It’s about the distribution of voting power, the timing of proposals, and the economic levers native tokens give holders. Short-term LP rewards, for instance, can concentrate tokens in the hands of yield optimizers who then participate in governance as a secondary use. This creates feedback loops.
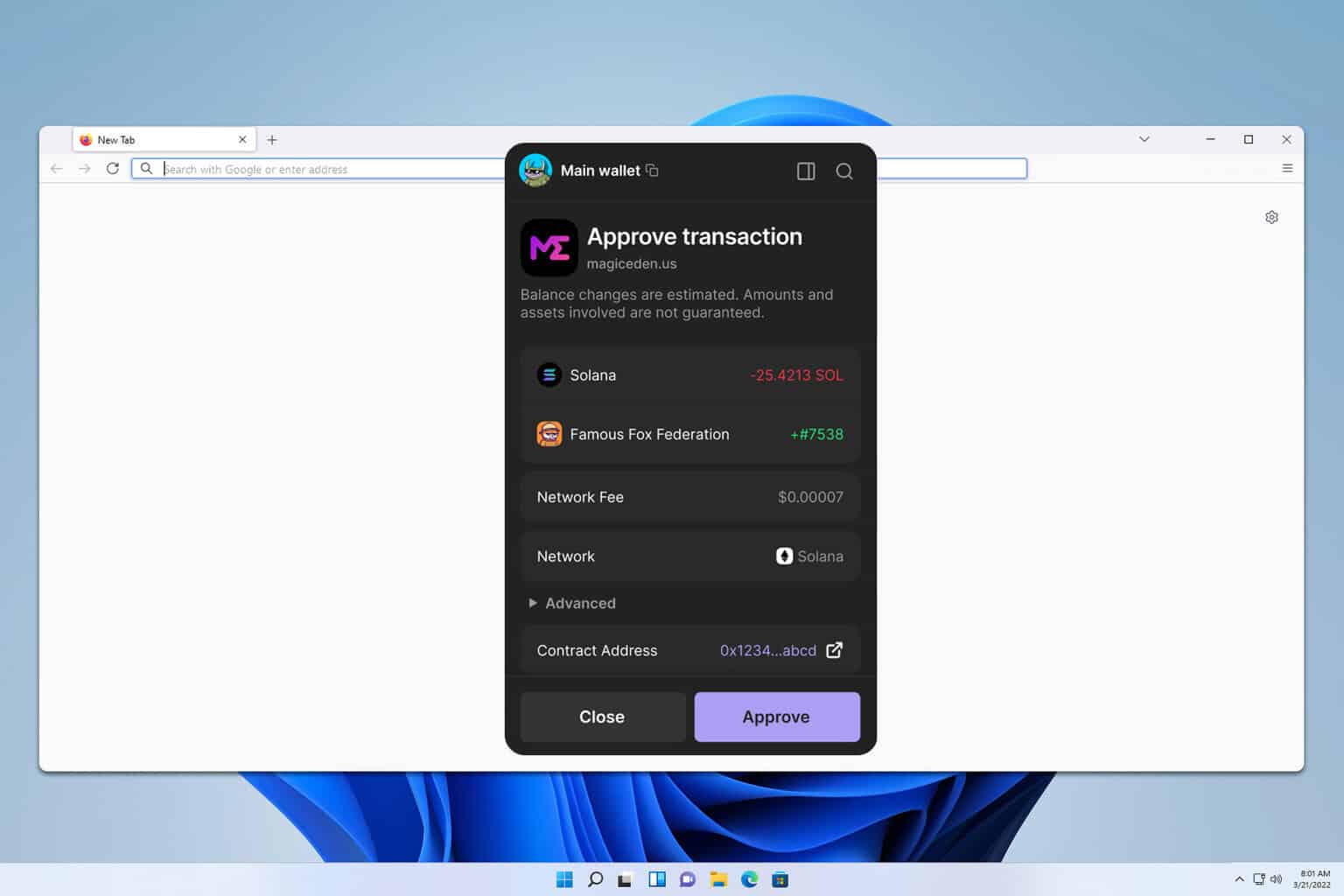
Mechanically, LBPs use two main levers: initial token weight and a schedule for weight change. Medium-sized pools can start heavily weighted toward the token being sold, making the initial price high. Over hours or days the protocol gradually lowers that weight, letting the token price trend downward. Long-term, that price path shapes who buys in and at what price—which in turn shapes governance seat allocation and proposal outcomes.
There are trade-offs. LBPs reduce immediate frontrunning but don’t eliminate MEV. They’re not a magic wand. I’m biased, but this part bugs me: teams often talk about fairness, but forget tactical liquidity incentives that benefit bots or well-funded participants. Something felt off about treating LBPs as full-proof “fair launch” tools when, in reality, they’re just one piece of a complex distribution puzzle.
On governance design, timelocks, quorum requirements, and delegated voting are where the nuance lives. Delegation helps participation numbers by letting active stewards vote on behalf of passive holders. But delegation can also lead to centralization if too many holders delegate to a few addresses. Initially I thought delegation would scale well. Though actually—when large LPs begin to delegate in bulk, the network concentrates influence, and that can squash minority voices.
For teams running launches, a layered approach usually works better: combine LBPs with vesting schedules, on-chain buybacks, and staggered governance token releases. This reduces the payoff for a single short-term actor trying to dominate the vote within the first week. It also creates room for community members to accumulate positions more slowly, and to signal intent rather than just chase yield.
Check this out—protocol tooling matters. Balancer’s flexible pool architecture is often used for LBPs because it supports dynamic weights and fee controls. For a hands-on reference, you can explore Balancer’s documentation and official resources here: https://sites.google.com/cryptowalletuk.com/balancer-official-site/ This isn’t a paid plug; it’s practical—if you’re designing an LBP you want protocol-level features that let you tweak schedules, fees, and governance knobs safely.
Risk management is critical. Short sentence. Impermanent loss still exists, and it bites token teams who retain liquidity for treasury use. Medium sentence here to explain. If a treasury holds LP tokens and the market rebalances, the treasury’s effective governance stake might shrink relative to active traders, which can be surprising—and costly—for long-term roadmaps.
Also—UX and information asymmetry are underrated. Long, complex proposals with buried code-level changes favor parties with engineering resources to audit and propose. On one hand, that expertise is needed to make safe changes. On the other, it tilts outcomes toward those with specialized capacity. That tension is real, and it shows up in debates about “off-chain signal votes” versus binding on-chain votes: signal voting helps inform but doesn’t prevent rapid on-chain changes from occurring later if the token distribution allows it.
Common questions
What is an LBP and why use one?
An LBP (Liquidity Bootstrapping Pool) is a pool that shifts token weights over time to enable price discovery and reduce early sniping. It tends to make initial prices less attractive to instant speculators and gives a broader set of participants a chance to buy in as weights normalize.
How does governance interact with liquidity providers?
LPs often hold governance tokens as part of their yield or as collateral. This creates alignment or conflict: LP incentives can push for short-term fee optimization while governance leans toward long-term protocol health. Design choices like vesting and delegation can help balance these motives.
What are practical anti-abuse measures?
Use staged token releases, multi-sig treasury controls, on-chain timelocks, and careful LBP parameterization. Also encourage active, informed voting by compensating governance participation—though beware of vote-buying side effects.